Overview
By default, Expedient configures clients with 2-factor authentication (2FA) to Expedient Secure User VPN with OneLogin as an identity provider. If preferred, a client can substitute OneLogin with alternative authentication options, including the firewall's local user database. However, the user account credentials and the authentication mechanisms are local to the firewall. Therefore, this authentication mechanism is not scalable and is less secure because it requires an account for every Global Protect user and is only advised for small deployments. If a client chooses to use an alternative authentication option, it is the client's responsibility to manage that solution. While Expedient may not manage these alternative solutions, Expedient provides this documentation to assist clients with getting a local user database setup for the Expedient Secure User VPN.
Prerequisites
The steps in this document assume you have already gathered the names and passwords for which you would like to associate with your local users.
Process
- Navigate to firewall UI after successfully authenticating into fw.expedient.cloud
- Once you have access, create the local user database
- Go to Device > Local User Database > Users to begin creating the local User Database
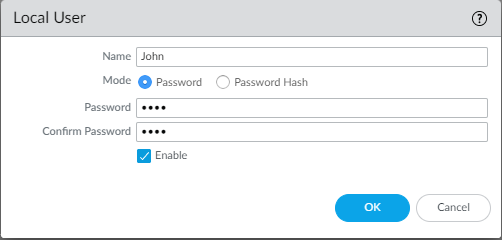
- Click +add and enter the user's name and password for use and then hit OK once done.
- Then create the Authentication Profile.
- Go to Device > Authentication Profile to start creating one
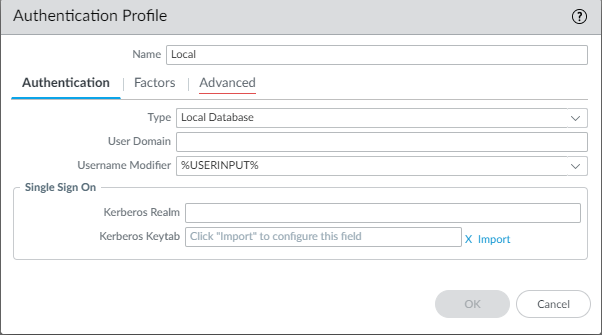
- Click +add enter in the name you want for the profile while in the authentication tab
- Change type to Local Database and leave the rest to defaults unless otherwise directed while in the authentication tab
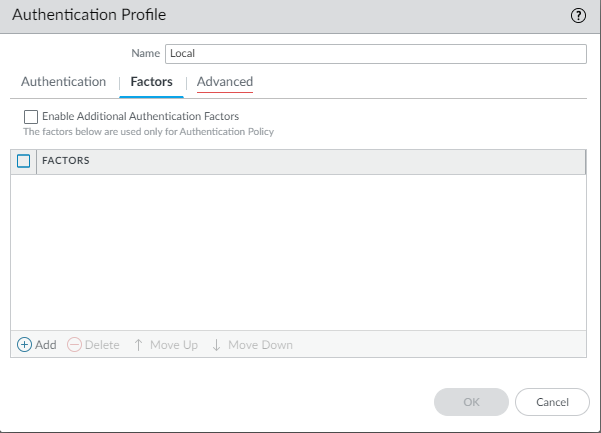
- The Factors tab can be left to defaults unless otherwise directed.
- The Advanced tab can set a user allow list or account lockout parameters.
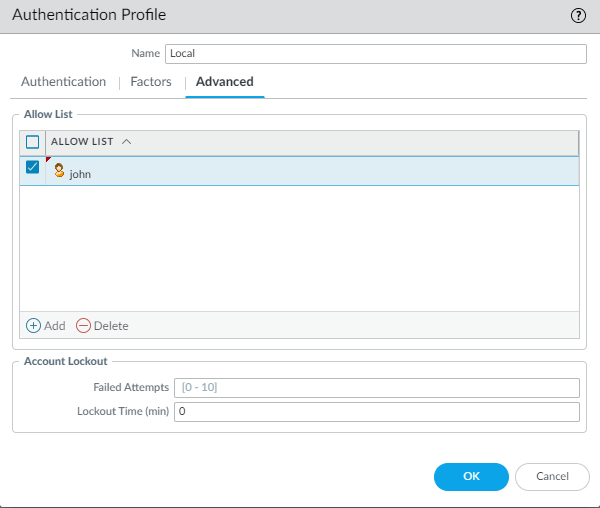
- Once complete, click OK
- The local user database can now be used under the Global Protect Portal and Gateway configuration when adding authentication methods.
Network > GlobalProtect > Portals > Select Portal > Authentication > Client Authentication > +Add
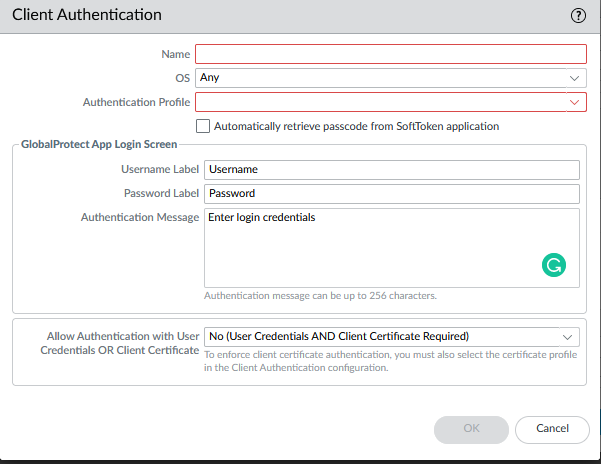
Network > GlobalProtect > Gateways > Select Gateway > Authentication > Client Authentication > +Add
3. Perform a firewall commit operation.
